Set up the Zero Trust Access App for iOS Devices
End users can access private resources from their Apple iOS mobile devices (iPhone or iPad) using the Zero Trust Access app. This Cisco Secure Client app uses Apple's platform-native zero trust network access technology.
Zero Trust Access app for iOS:

Table of Contents
- System Requirements
- Guidelines and Limitations
- Configure Settings in Cisco Secure Access
- Install the App
- Have End Users Enroll in Zero Trust Access
- Notes for administrators
System Requirements
Apple iPhone or iPad running iOS 17.2 or later
Guidelines and Limitations
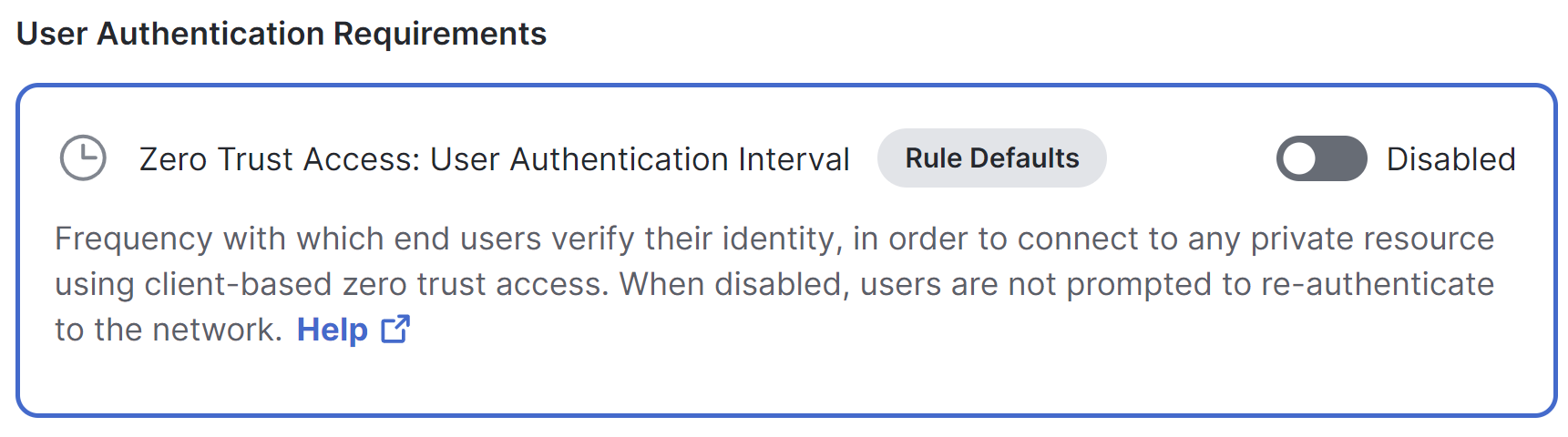
- iOS does not currently support step-up authentication, so users will not be able to use the Zero Trust Access app to access a private resource if step up authentication is enabled for that resource. You can disable this functionality by default on the Rule Defaults page, or disable it in private access rules that include access for iOS devices:
For information, see Network Authentication for Zero Trust Access.
- Traffic originating from the iOS client has an implicit subdomain wildcard on every rule. So, for example, if a resource is configured with the address “foo.com”, iOS traffic to that resource will also match “bar.foo.com.” Configure your private resources and rules accordingly.
Configure Settings in Cisco Secure Access
Ensure that private resources can be accessed using Zero Trust Access from supported endpoint OS versions:
- Configure a client-based posture profile that includes iOS devices and supported iOS versions:
Navigate to Secure > Endpoint Posture Profiles.
For information, see Add a Client-Based Zero Trust Access Posture Profile. - Ensure that each applicable private resource is configured to allow client-based Zero Trust Access connections.
For information, see Add a Private Resource. - Ensure that a network tunnel group or resource connector group is configured to send ZTA traffic to this resource.
Navigate to Connect > End User Connectivity.
For information, see Manage Network Connections. - Configure a private access rule that allows traffic to the applicable private resources using the posture profile you configured in Step 1.
- Ensure that the end user is configured for single sign-on authentication (SSO).
Install the App
There are two ways to distribute the app to IOS devices:
- You or end users can obtain the app from the App Store
- You can use your EMM/MDM vendor ecosystem
Have End Users Enroll in Zero Trust Access
The Zero Trust Access client app will walk end users through the enrollment process, which they should find reasonably straightforward.
You can give your end users the following instructions for (if applicable) installing the app and enrolling in Zero Trust Access:
- If your administrator has not yet installed the Zero Trust Access app on your device:
Install the app from the App Store. - In order to enroll your device for Zero Trust Access, you will need your work email address and your single sign-on credentials.
- Launch the app and follow the instructions.
- Important! In order to avoid unpredictable disruptions when accessing your organization's resources, you should allow notifications.
- You will be prompted to sign in using Single sign-on credentials.
- When you see an Approve prompt, verify that the information on the screen is correct, then tap Approve.
- You may need to sign in again the first time you access an application on your network.
- You may be required to sign in again periodically in order to access applications on your network. This is expected.
Notes for administrators
- The enrollment process recommends that users allow notifications. Notifications keep users up-to-date on Zero Trust Access and allows the Zero Trust Access application to communicate with the backend relay configuration.
- To monitor and troubleshoot client-based zero trust access connections from mobile devices, see Monitor and Troubleshoot Zero Trust Access from Mobile Devices.
Get Started and Manage Client-based Zero Trust Access from Mobile Devices < Set up the Zero Trust Access App for iOS Devices > Set up the Zero Trust Access App for Android Devices
Updated 8 months ago
