View Zero Trust Events in Activity Search Report
The Activity Search report includes the full details about the Zero Trust Access traffic events in your organization. For more information about the Activity Search report, see View the Activity Search Report.
Note: If you assign Block to a rule that is destine for a private application and there is an HTTPS “Get” request for a downloadable file, the rule blocks matching traffic and actions appropriately but the event appears in Activity Search twice: one entry as the action is “blocked” and one entry as the action is “allow”. Activity Search does not currently condense events that generate multiple entries and thusly increases the hit counter as “2”.
Table of Contents
Prerequisites
- A minimum user role of Read-only. For more information, see Manage Accounts.
Procedure
- Navigate to Monitor > Reports > Activity Search.
- Choose a time frame to view the report. You can view the results for the last 24 hours (default), Yesterday, Last 7 Days, Last 30 Days, or a Custom range.
- From the Requests menu, choose a request type or the default of All. Filters update to those that are relevant to the type of request chosen.
- For an item in the report, click on the ellipsis (...). Click View Full Details to display the details of the Zero Trust Access event.
Event Details
View the Zero Trust event details in the Activity Search report.
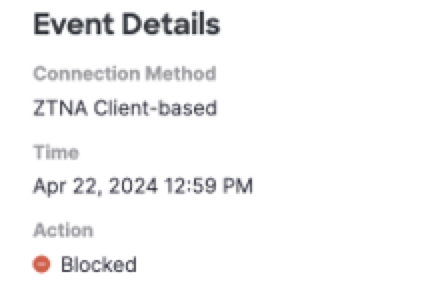
| Field Name | Description |
|---|---|
| Connection Method | The type of connection method: ZTA Client-based or ZTA Browser-based. |
| Time | The time of the event. |
| Action | Indicates if the traffic was blocked or allowed. |
Access Details
View the Zero Trust access details in the Activity Search report.
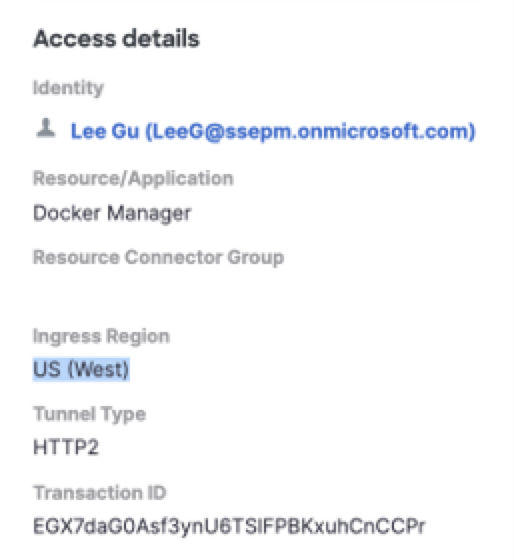
| Field Name | Description |
|---|---|
| Identity | The name and email of the user identified in the Zero Trust connection event. |
| Ingress Region | The geographic region of the data center where Secure Access received the incoming traffic. |
| Resource/Application | The name of the private application. |
| Zero Trust Access Profile | The name of the Zero Trust Access Profile used in the event. |
| Trusted Network | The trusted network identified in the connection, disconnection, or evaluation of a policy-triggered event. |
| Egress IP | The IP address used when traffic exits a network or system to reach the destination outside of it. |
| Resource Connector Group | The ID of the resource connector group that provides access to the private resource. |
| Tunnel Type | The type of traffic supported by the network tunnel, which the endpoint established with the proxy. The transport protocol on the tunnel is either HTTP or HTTP3. |
| Transaction ID | The unique ID associated with the Zero Trust connection request. Use the transaction ID to correlate and troubleshoot connection issues. |
Block Details
View the Zero Trust block details in the Activity Search report.
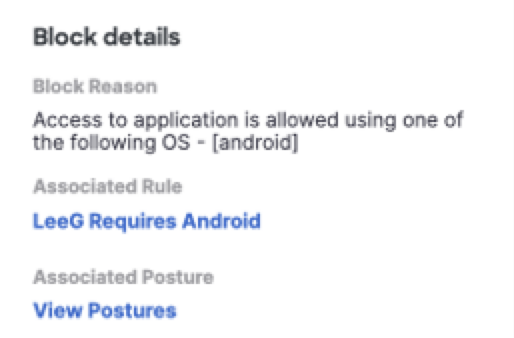
| Field Name | Description |
|---|---|
| Block Reason | Secure Access provides an explanation for blocking access to the private resource. |
| Associated Rule | When access was blocked for not meeting access or posture requirements, Secure Access reports the closest matched policy rule that would have allowed access. |
| Associated Posture Profile | The posture profile that is configured for the associated rule. |
Endpoint Details
View the Zero Trust endpoint details in the Activity Search report.
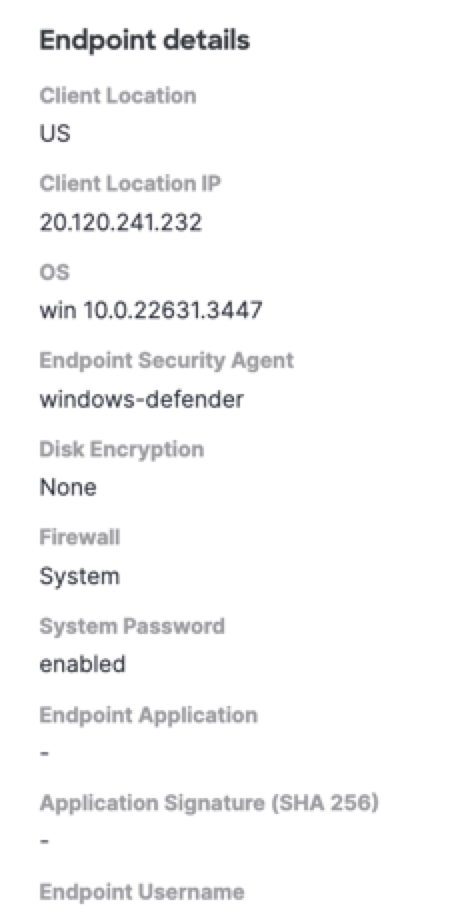
| Field Name | Description |
|---|---|
| Client Location | The two-character country identifier. |
| Client Location IP | The IPv4 or IPv6 address of the client. Supports both compressed and long-form IPv6 address formats. |
| OS | The operating system of the client's device. |
| Endpoint Security Agent | The name of the endpoint security agent. |
| Disk Encryption | Indicates if the client's device has disk encryption. |
| Firewall | Indicates if the client environment has a firewall enabled. |
| System Password | Indicates if the client has a system password enabled. |
| Endpoint Application | The name of the endpoint application, which initiated the connection. |
| Application Signature | The SHA256 signature of the endpoint application process. |
| Endpoint Username | The username that is associated with the endpoint application process. |
View Web Events in Activity Search Report < View Zero Trust Events in Activity Search Report > View Activity Search Report Actions
Updated 20 days ago
