Control Access to Custom URLs
Adding custom URLs to a destination list allows Secure Access to extend a domain in a destination list to encompass full URLs. This allows you to control access to a web site's pages based on the full URL of that portion of the web site pages.
Table of Contents
Prerequisites
- Install a root certificate to support SSL decryption of URLs.
- The custom URL destination list is protocol-agnostic. This means that Secure Access does not expect that it's possible to know which protocol a web site will use in advance. Therefore, adding a protocol in front of a URL is not required when defining a destination list. Instead, with SSL decryption enabled, Secure Access can block a URL whether it's HTTP or HTTPS and thus minimize the difficulty of creating a destination list. For more information, see Manage Certificates.
Block a URL
To block a URL, you can add it to a blocked destination list or create a new blocked destination list for URLs.
To add a URL to an existing blocked destination list:
- Navigate to Secure > Access Policy.
- Expand a destination list
- Add a URL.
- Click Save.
Note: It is important to specify the URL correctly so that what’s in your policy rule matches what the user is trying to access and is controlled correctly by access settings (block, allow, or warn—depending on the policy type).
URL Normalization
URLs normalize automatically using the following criteria:
| URL Normalization | |
|---|---|
| Protocol Schema (the protocol should be stripped) | hxxp://xyz.com/test → xyz.com/test |
| Username: Password (should be stripped) | user:[email protected] → xyz.com |
| Ports (should be stripped) | xyz.com:8080/abc → xyz.com/abc |
| Trailing slashes (stripped from the end of the URL) | xyz.com/abc/ → xyz.com/abc |
URL Normalization for Destination Lists
URL filtering conforms to URL normalization standards. Certain guidelines must be followed to ensure that the URL you are entering is what you want to block or allow. These can sometimes mean that the way a URL is displayed in the browser's address bar is not how it should be specified in a destination list. This is not done automatically. You must format the URL using the guidelines listed here for it to be blocked or allowed as intended. For guidelines, see URL Normalization.
Troubleshooting Unblocked URLs
If the Secure Access block page does not display when navigating to a URL you expect to be blocked, ensure that the policy rule with the destination list enabled is higher in order than other rules that the enrolled resources may be part of.
Wait up to five minutes before testing again after any changes are made to ensure that enough time has passed for the changes to be replicated throughout Secure Access.
If problems persist, clear the local browser cache on your machine. Alternatively, clear your machine's DNS cache—a reboot will accomplish this.
Also, check to see if you have a local—on-premise—proxy that is interfering.
Additionally, confirm that you have installed certificates. For more information, see Manage Certificates.
Reporting for Blocked URLs
The Secure Access Activity Search report supports the use of URLs as a search filter.
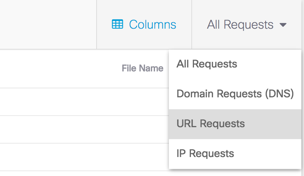
After you've filtered for URLs, add another filter to show the custom block URLs that belong to your destination lists.
Examples
The following examples show a single URL and what you can and cannot enter to have a block of that URL enforced. The list of URLs is built out from a single example, modifying a single parameter to show whether the URL "//a.co/cx/15195/100/setup_1848x19m.exe?z=z&super=bad&test=yes" would be blocked based on a URL.
In these examples, the protocol is stripped as it would be by the interface.
If you wanted to block this URL a.co/cx/15195/100/setup_1848x19m.exe?z=z&super=bad&test=yes the following logic would apply.
| URL | Blocked? | Reason |
|---|---|---|
| a.co/cx/15195/100/setup_1848x19m.exe?z=z&super=bad&test=yes | Yes | The full URL is entered. |
| a.co/cx/15195/100/setup_1848x19m.exe?super=bad&test=yes&z=z | Yes | "&" is a delimiter; therefore, it's added as another level to the URL after the word "yes". |
| a.co/cx/15195/100/setup_1848x19m.exe?super=bad&test=yes | No | "?" is a delimiter so the URL still would begin at the "yes" and any enforcement would happen after that. |
| a.co/cx/15195/100/setup_1848x19m.exe? | No | Given the "?", it still means only characters after "yes" will be enforced; therefore, a direct download of this file would be allowed. |
| a.co/cx/15195/100/setup_1848x19m.exe | No | We will still only block any paths after "yes"; therefore, a direct download of this file would be allowed. |
If you want to block this URL g.com/a/d, the following logic applies.
Note: These are only examples of destination list entries that would and would not block the URL g.com/a/d.
| URL | Blocked? | Reason |
|---|---|---|
| g.com/a/d | Yes | The full URL is entered. |
| g.com/a/d?g | Yes | Delimits the path with the query "g" but still just a delimiter thus this will be enforced. |
| g.com/a/d? | Yes | URL + the "?" delimiter. |
| g.com/a/ | No | The URL ends with "/d" so anything before "/d" would not be enforced. |
| g.com/a/?a | No | The URL ends with "/d" so anything before "/d" would not be enforced. |
If you want to block this URL d.co/cx/15195/100, the following applies.
Note: These are only examples of which destination list entries would block the URL "d.co/cx/15195/100" and which would not.
| URL | Enforced | Reason |
|---|---|---|
| d.co/cx/15195/100 | Yes | The full URL is entered. |
| d.co/cx/15195/100/? | Yes | Everything after the delimited "/" after 100 would be blocked. |
| d.co/cx/15195/100/ | Yes | Everything after the delimited "/" after 100 would be blocked. |
| d.co/cx/15195/100 | Yes | Everything after the delimiting "/" after 100 would be blocked. |
| d.co/cx/15195/10 | No | The delimiter is only for paths after the "/" so any changes to the final path of /100/ would be ignored. |
| d.co/cx/15195/1000 | No | The delimiter is only for paths after the "/" so any changes to the final path of /100/ would be ignored. |
| d.co/cx/15195/ | No | The delimiter is only for paths after the "/" so any changes to the final path of /100/ would be ignored. |
| d.co/cx/15195 | No | The delimiter is only for paths after the "/" so any changes to the final path of /100/ would be ignored. |
Note: There are normalization rules that most administrators never encounter. If you find that a URL is not being properly filtered and you've confirmed that all criteria are met, see the URL Normalization RFC.
Troubleshooting
If you encounter issues with the custom URL feature, contact Support and include the output of the following commands:
macOS
dig proxy.opendnstest.com
dig debug.opendns.com txt
Windows
nslookup proxy.opendnstest.com
nslookup -type=txt debug.opendns.com
Download Destinations to a CSV File < Control Access to Custom URLs > Control Access to Domains
Updated 21 days ago
