Enable Cloud Malware Protection for AWS Tenants
Secure Access supports Cloud Malware protection for files within your AWS deployment. To enable this feature:
- Enable CloudTrail Event Logging for S3 Buckets and Objects from the AWS console. (You need only enable this feature once for your account; you need not do it for each AWS tenant you authorize.)
- Authorize an AWS Tenant in Secure Access.
- Create an AWS Stack from the AWS console.
An AWS account can support at most one SaaS API DLP tenant and one Cloud Malware tenant at the same time. You cannot authorize multiple Cloud Malware tenants for a single AWS account.
Table of Contents
- Prerequisites
- Limitation
- Enable CloudTrail Event Logging for S3 Buckets and Objects
- Obtain Your AWS Account ID
- Authorize an AWS Tenant
- Create an AWS Stack
- Revoke Authorization
Prerequisites
- Full Admin user role. For more information, see Manage Accounts.
- You must have an active AWS tenant and the person doing the installation must be an AWS Administrator.
- You must Enable CloudTrail Event Logging for S3 Buckets and Objects for your AWS account. (You need enable this feature only once for your account; you need not do it for each AWS tenant you authorize.)
- You must Obtain your AWS Account ID .
- Chrome or Firefox is recommended with pop-up blockers/ad blockers disabled (only for the duration of authorization).
Limitation
- A tenant that fails to authenticate cannot be deleted.
Enable CloudTrail Event Logging for S3 Buckets and Objects
You must enable CloudTrail event logging to provide you with a record of activities in your AWS account. You need enable this feature only once for your account; you need not do it for each AWS tenant you authorize.
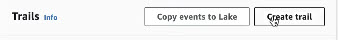
- In the AWS console, navigate to CloudTrail and choose Create Trail.
- Provide a meaningful Trail name for your trail.
- Under Events, choose Data Events to log data events.
- For Storage location, choose Use existing S3 bucket, and choose Browse to choose an S3 bucket in your account.
- You may optionally choose to enable Log file SSE KMS encryption for your log files. (If you choose this option, see Step 11.)
- On theChoose log events page, choose Data events.
- For Data event source choose S3.
- You can choose from:
- Log all current and future S3 buckets (This is the default.)
Choose to log Write events.
- Individual bucket selection (This can be a more economical choice.)
Browse for existing buckets and click Add bucket to log data events for each. Choose to log Write events.
- For the remaining options in the CloudTrail creation wizard, choose the settings appropriate to your environment.
- On the Review and Create page, review your choices and Edit if necessary. Then click Create Trail.
- If in Step 5 you chose to enable Log file SSE KMS encryption for your log files, grant permission for the encryption key to the role CiscoSecureAccessScanner. In the AWS console, under Key Management Service (KMS) > Customer managed keys > Key ID > Edit key policy, add a statement to grant permission for the role CiscoSecureAccessScanner.
- If your S3 buckets have restrictive policies associated with them, add statements to those policies to grant the role CiscoSecureAccessScanner access to those buckets. In the AWS console, see Amazon S3 > Buckets > Bucket Name > Permissions > Bucket Policy.
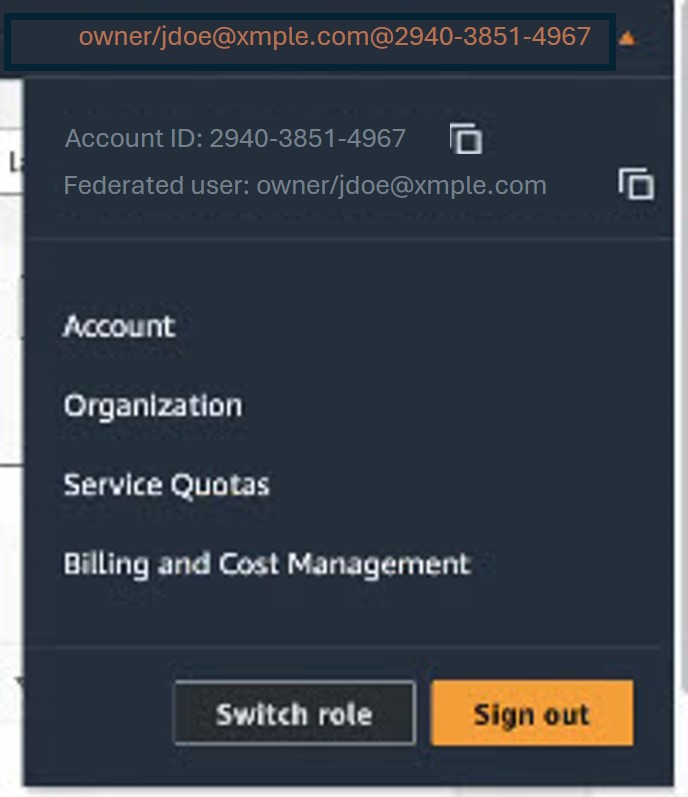
Obtain Your AWS Account ID
- Log in to the AWS Management Console with an Admin account.
- In the navigation bar at the upper right, click on your user name. The account ID is displayed above your user name.
- Click the Copy icon to the right of the Account ID to copy it.
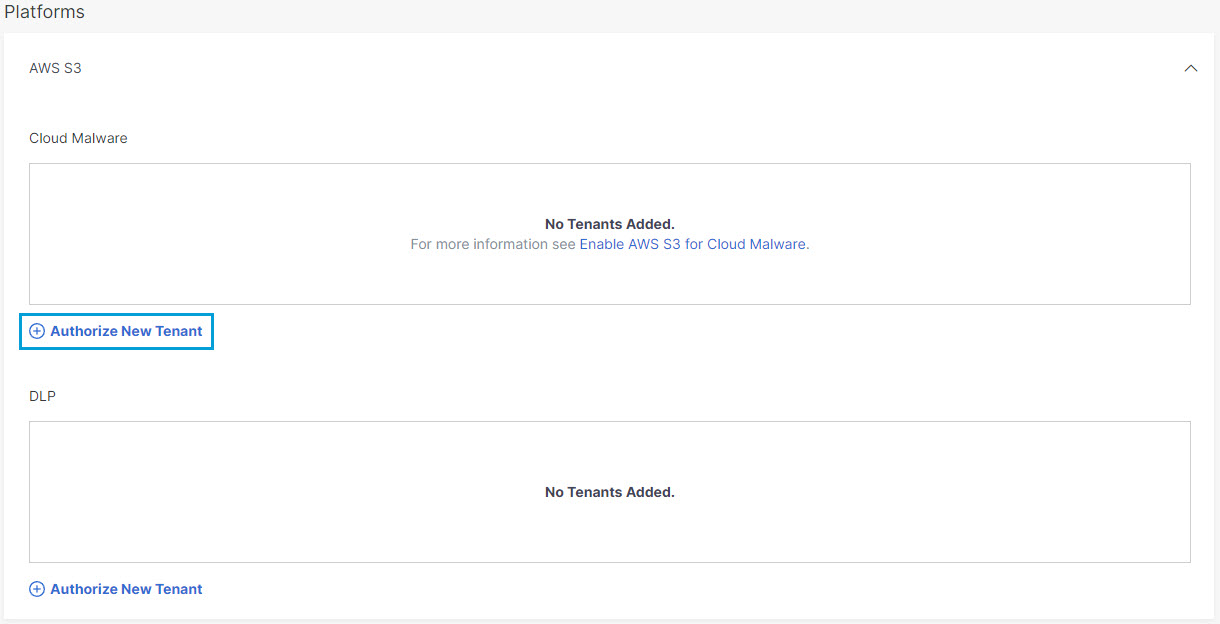
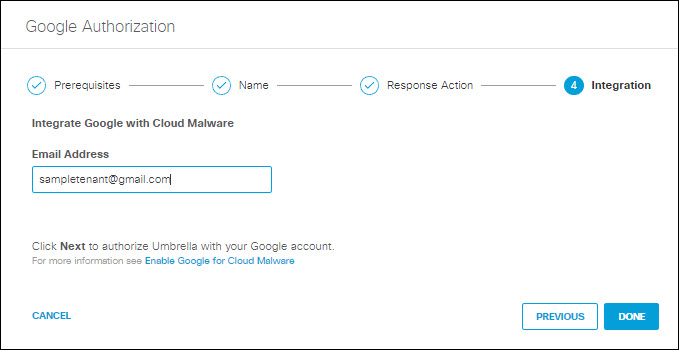
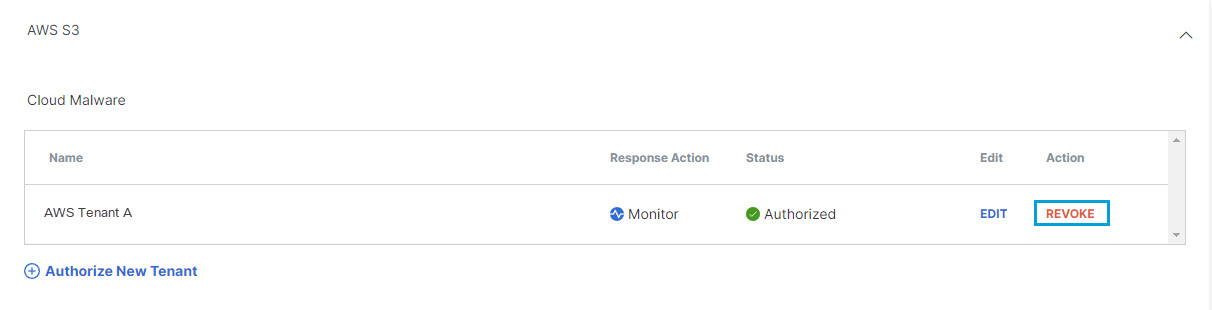
Authorize a Tenant
- Navigate to Admin > Authentication.
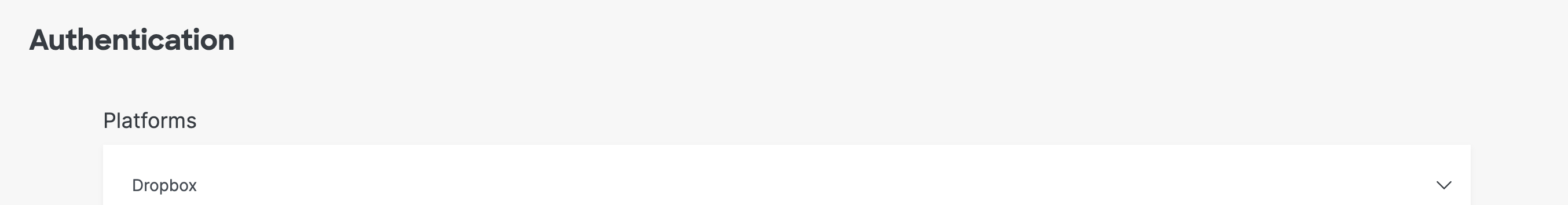
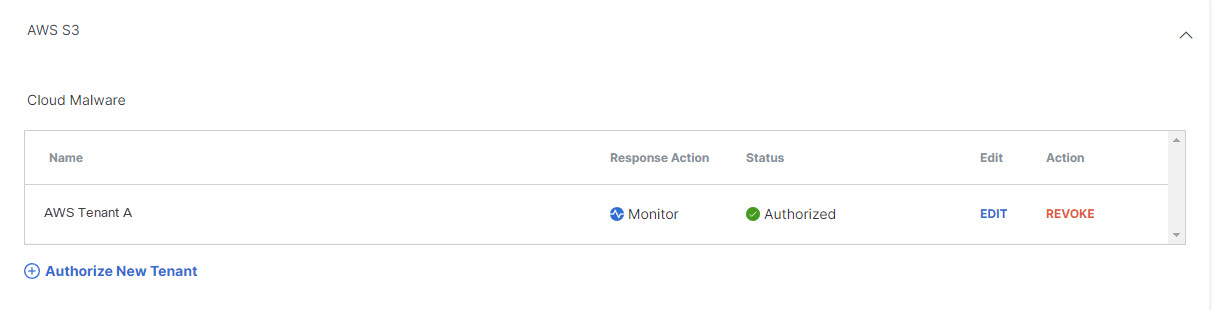
- Under Platforms, click to expand AWS S3.
- Under Cloud Malware click Authorize New Tenant to add an AWS S3 tenant to your Secure Access environment.
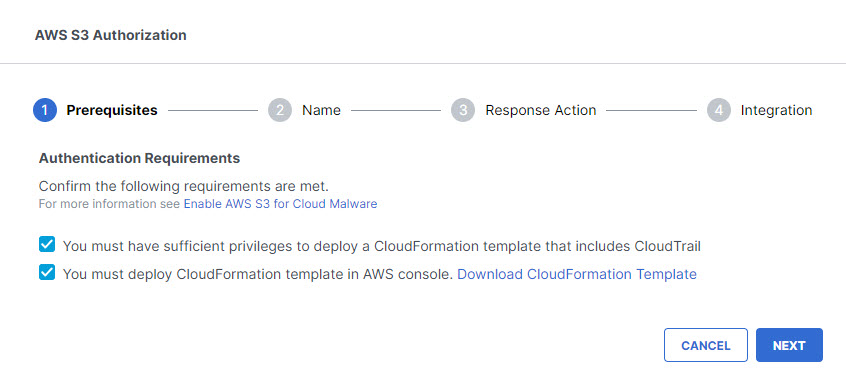
- In the AWS S3 Authorization dialog box, click Download CloudFormation Template to download an AWS CloudFormation template named aws-cisco-template.json. Save the template to your local machine, then Create an AWS Stack before proceeding to the next step.
Note: If you enable both Cloud Malware and DLP protection for a tenant, a single stack can serve for both purposes. If you have already created an AWS stack for DLP protection for this tenant, you need not create another stack.
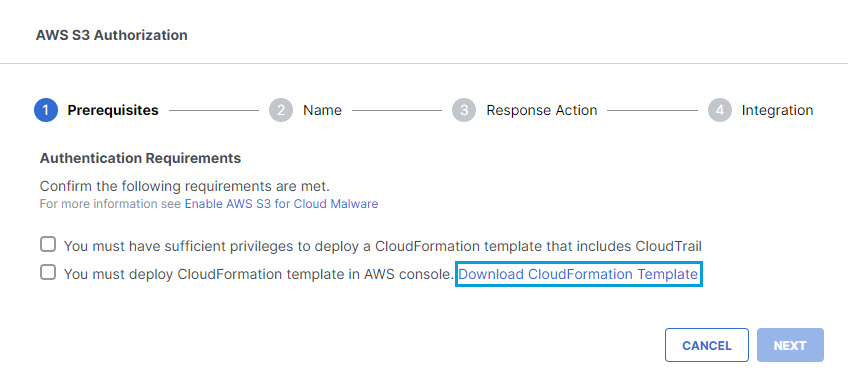
- In the AWS S3Authorization dialog box, check the checkboxes to verify you meet the prerequisites, then click Next.
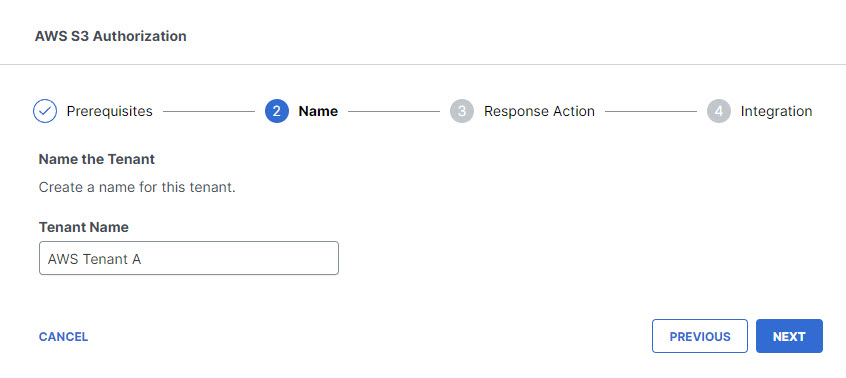
- Provide a name for your tenant that is meaningful within your environment, then click Next.
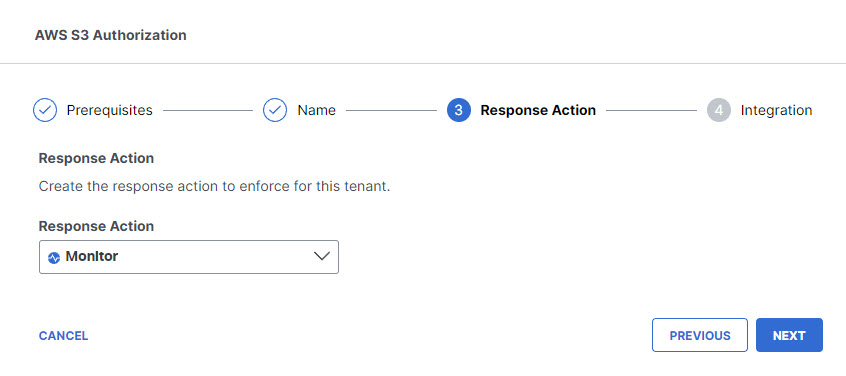
- Choose Monitor for the Response Action for Secure Access to apply to AWS S3files found with malware, then click Next.
- Paste your AWS Account ID in the text box, confirm that you have used the CloudFormation template to create an AWS stack, then click Done.
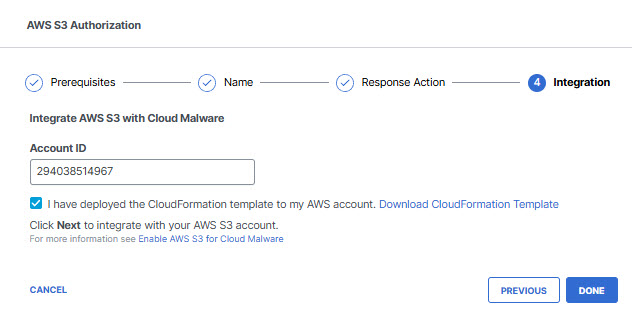
- The new tenant will appear on the Authorization page in the list under AWS S3.
Create an AWS Stack
Secure Access requires an AWS stack to monitor and communicate with your S3 resources. If you have more than one AWS tenant, you will need a stack for each tenant. If you enable both Cloud Malware and DLP protection for a tenant, a single stack can serve for both purposes.
NOTE: If you enable both Cloud Malware and DLP protection for an AWS tenant, and then disable one of those two forms of protection, you must leave the stack intact to support the remaining protection.
Important:Perform this task after you have downloaded a CloudFormation Template in Step 4 of Authorize an AWS Tenant. Once you have created the stack, return to Step 5 of that task.
For more information about AWS Stacks, see the Amazon AWS Cloud Formation User Guide.
- Log in to the AWS Management Console with an Admin account.
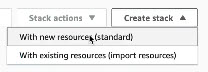
- In the AWS console, navigate to CloudFormation > Stacks and choose Create new stack > With new resources.
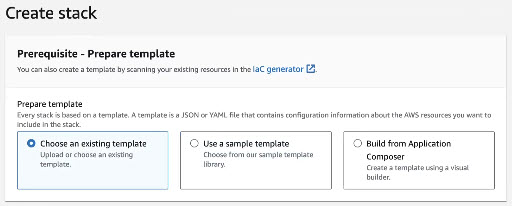
- On the Create stack page, under Prerequisite - Prepare template, select Choose an existing template.
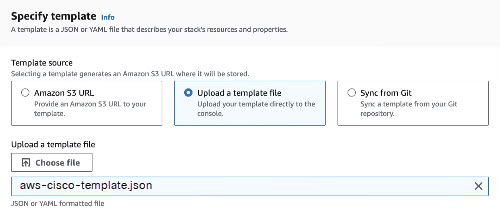
- On the Create stack page, under Specify template, select Upload a template file, then click Choose file and navigate to and select the JSON file (aws-cisco-template.json) on your local system which you downloaded when you authorized the AWS tenant in Secure Access.
- (Optional) Click View in Application Composer to open a new tab displaying a graphical representation of the stack deployment.
- Click Next.
- For the remaining options in the stack creation wizard, choose the settings appropriate to your environment. We recommend the following best practices:
- Provide a stack name that is meaningful within your environment.
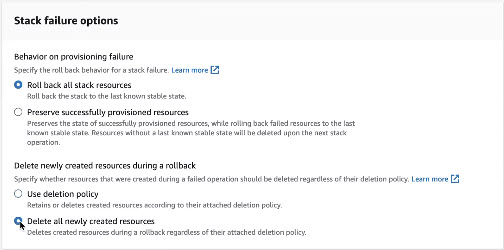
- Under Stack failure options, choose Role back stack resources and Delete all newly created resources.
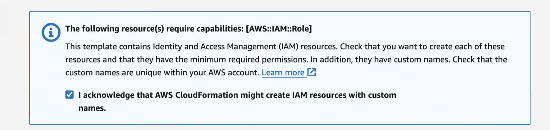
- Acknowledge that AWS CloudFormation may create IAM resources with custom names within your AWS account.
- Click Submit.
- In the AWS console the status of all stack in your account is displayed under CloudFormation > Stacks. Wait until the status for your new stack is displayed as CREATE_COMPLETE.
- Continue with Step 5 of Authorize an AWS Tenant.
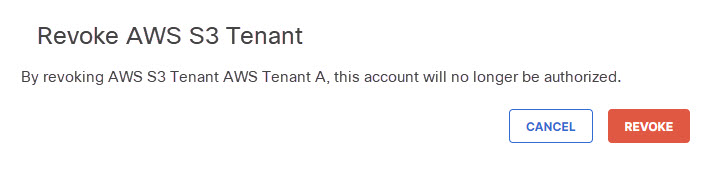
Revoke Authorization
- Navigate to Admin > Authentication.
- In the Platforms section, click AWS S3.
- Under the Action column, click Revoke. You can revoke any authorized tenant.
- Confirm to proceed. The selected tenant will no longer be authorized.
Consider deleting the AWS stack you created if it is not needed for other purposes.
Revoke Authorization for a Platform < Enable Cloud Malware Protection for AWS Tenants > Enable Cloud Malware Protection for Azure Tenants
Updated about 1 month ago