Provision Users and Groups from Microsoft Entra ID
Cisco Secure Access supports the provisioning of users and groups from Microsoft Entra ID (formerly Azure Active Directory).
This guide describes how to add your Secure Access System for Cross-domain Identity Management (SCIM) token to the Cisco User Management for Secure Access app in the Microsoft Entra ID portal and provision users and groups to Secure Access through the app.
Table of Contents
- Prerequisites
- Limitations
- Procedure
- Configure Guest Users
- View Provisioned Users and Groups in Secure Access
- Refresh SCIM Token
Prerequisites
- Full Admin user role. For more information, see Manage Accounts.
- A valid Microsoft Entra ID subscription with a premium Microsoft Entra ID license.
- Add the IdP in Secure Access and generate a valid SCIM token. For more information, see Add a Cloud Identity Provider.
- No concurrent provisioning of the same users or groups from on-premises AD or Microsoft Entra ID. If you are using the on-premises Cisco AD Connector to import users and groups and choose to import the same users and groups from Microsoft Entra ID, ensure that the on-premises Cisco AD Connector is switched off or that the Cisco AD Connector service on the connector machine is stopped.
- For IP-to-user mapping deployments, you must use the on-premises Cisco AD Connector. Microsoft Entra ID does not store the private IP to Active AD user mappings.
- Import the
ObjectGUIDattribute from Microsoft Entra ID to Secure Access. The on-premises Cisco AD Connector and Cisco Secure Client rely on theObjectGUIDattribute for user identification. If all of your endpoints have the Cisco Secure Client deployed, you do not have to import theObjectGUIDattribute from Microsoft Entra ID.- Before you set up the import of the
ObjectGUIDattribute, ensure that the on-premises Cisco AD Connector that is synchronizing these identities is switched off or that the Cisco Connector service on the connector machine is stopped. - To ensure that the
ObjectGUIDattribute for users is synchronized from Microsoft Entra ID to Secure Access, your endpoints must authenticate against on-premises AD and run the Cisco Secure Client. For more information about importing theObjectGUIDattribute for users, see Tutorial: Configure Cisco Secure Access User Management for automatic user provisioning.
- Before you set up the import of the
- If you previously configured access rules that included groups imported from on-premises AD, and then choose to import the same groups from Microsoft Entra ID, you must reconfigure the access rules to map the Microsoft Entra ID groups instead of the on-premises AD groups. In an access rule, on-premises AD group names are displayed with the domain name preceding the group name, for example: Domain1\ADGroup1. For Microsoft Entra ID, only group names are displayed, for example: ADGroup1.
Limitations
- You can provision a maximum of 1000 groups from Microsoft Entra ID to Secure Access. Secure Access supports the provisioning of an unlimited number of users from Microsoft Entra ID. For more information, see Limitations and Range Limits.
- Concurrent synchronization of the same users and groups from the Cisco AD Connector and the Cisco User Management for Secure Access app is not supported and leads to inconsistent access rule enforcement.
- To ensure that all users are provisioned, create a dynamic All Users group and assign this group to the Cisco User Management for Secure Access app. For more information, see Dynamic Membership Rules for Groups in Azure Active Directory. You can assign additional groups as required for group-based access rule enforcement.
- Guest users invited to your Microsoft Entra ID tenant are provisioned to the same Secure Access user group as all other users provisioned by Microsoft Entra ID. Since members of the same user group inherit the same access rules in Secure Access, this may result in your Entra ID guest users gaining access to resources intended only for your Entra ID member users.
- Provisioning large numbers of users and groups to Secure Access may take several hours.
- Microsoft Entra ID does not support nested group memberships for group-based assignment to any SaaS application.
- After the initial provisioning of users and groups, Microsoft Entra ID synchronizes changes to Secure Access once every 40 minutes. Synchronization of updates to identities from Microsoft Entra ID to Secure Access may take up to one hour.
Procedure
Configure the Cisco User Management for Secure Access app and begin to provision users and groups from Microsoft Entra ID to Secure Access. For more information, see Tutorial: Configure Cisco Secure Access User Management for automatic user provisioning.
Note: Secure Access does not require the Cisco Active Directory (AD) Connector to provision users and groups from Microsoft Entra ID.
Configure Provisioning in Microsoft Entra ID
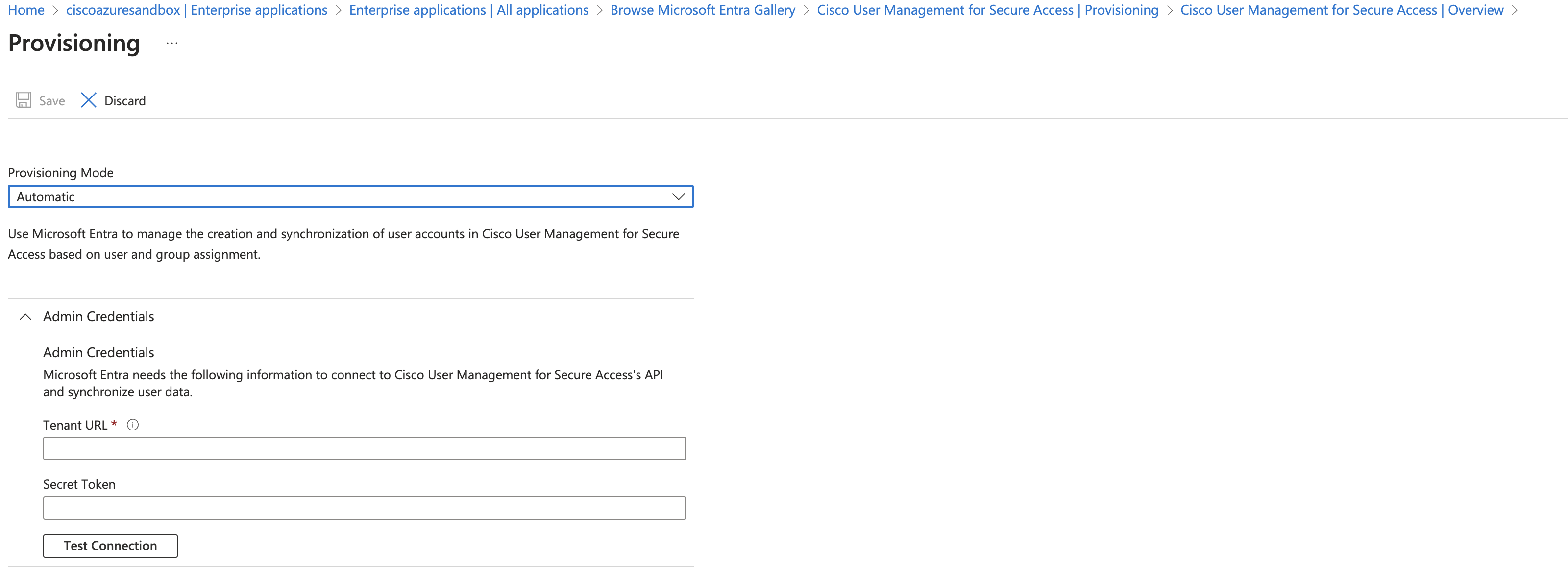
With your Secure Access SCIM token and API Identity URL, set up the Cisco User Management for Secure Access app on Microsoft Entra ID and provision users and groups.
- In Microsoft Entra ID, navigate to the Cisco User Management for Secure Access app.

- Add your Secure Access SCIM API token to the Secret Token field.
- Add the Secure Access API Identity URL to the Tenant URL field.
- Click Test Connection to confirm that you can use your Secure Access SCIM token to connect the Secure Access API with Microsoft Entra ID.
- Complete the steps to provision users from Microsoft Entra ID to Secure Access. For more information, see Tutorial: Configure Cisco Secure Access User Management for automatic user provisioning.
Review the user attributes that are synchronized from Microsoft Entra ID to the Cisco User Management for Secure Access app in Attribute Mappings. The attributes selected as Matching properties are used to match the user accounts in Cisco User Management for Secure Access app for update operations. If you choose to change the matching target attribute, ensure that the Cisco User Management for Secure Access app supports filtering users based on that attribute. - Click Save.
Supported Attributes for Users
| Cisco Attributes for Users | Microsoft Entra ID Attributes |
|---|---|
| userName | userPrincipalName |
| active | Not([IsSoftDeleted]) |
| displayName | displayName |
| name.givenName | givenName |
| name.familyName | surname |
| name.formatted | Join(" ", [givenName], [surname]) |
| externalId | objectId |
Supported Attributes for Groups
| Cisco Attributes for Groups | Microsoft Entra ID Attributes |
|---|---|
| displayName | displayName |
| externalId | objectId |
| members | members |
Configure Guest Users
To provision a guest user from Microsoft Entra ID to Secure Access, sign into the Cisco User Management for Secure app in Microsoft Entra ID and associate the Cisco userName attribute with the Microsoft Entra ID originalUserPrincipalName attribute.
-
In Microsoft Entra ID, navigate to the Cisco User Management for Secure Access app.
-
Navigate to Attribute Mappings.
-
Click Add New Mapping.
-
Add a mapping for userName to originalUserPrincipalName.

-
Click Save.
View Provisioned Users and Groups in Secure Access
- Navigate to Connect > Users and Groups to view the users and groups provisioned from Entra ID.
- For more information, see View User Details.
- For more information, see View Group Details.
Refresh SCIM Token
To avoid disrupting the provisioning of users and groups, we recommend that you refresh the SCIM token in Secure Access at least once every 90 days and immediately copy the new token to the Cisco User Management for Secure Access app in Microsoft Entra ID. For more information about generating the SCIM token, see Add a Cloud Identity Provider.
The administrators in the Secure Access organization are responsible for refreshing the SCIM token. Secure Access does not perform this action.
Provision Users and Groups from Okta < Provision Users and Groups from Microsoft Entra ID > Provision Users and Groups from Active Directory
Updated 24 days ago
