Configure Protected Networks for Roaming Devices
The Secure Access redirection setting for roaming device manages and protects the traffic from the Umbrella roaming client or the Cisco Secure Client when the roaming device is on a protected network or located off the protected network.
Roaming Devices on a Protected Network
- Roaming devices are protected by an organization's on-network policy's settings.
- The traffic sent from the roaming device is identified by the network identity in the Activity Search report.
- The Umbrella roaming client or the Cisco Secure Client is managed by Secure Access and is disabled. DNS settings revert to the DNS server configured for the network.
- DNS traffic from the roaming device is not encrypted.
Roaming Devices Off-Network
- Roaming devices are protected by an organization's off-network policy's settings.
- The traffic sent from the roaming device is identified by the roaming device identity in the Activity Search report.
- The Umbrella roaming client or the Cisco Secure Client is managed by Secure Access and is enabled.
- DNS traffic from the roaming device is encrypted.
Table of Contents
Prerequisites
- Full admin access to the Secure Access dashboard. See Manage Accounts.
Before You Begin
- Configure and add your networks in Secure Access. For more information, see Add a Network Identity.
- Install and configure the Umbrella roaming client or Cisco Secure Client on your roaming devices. For more information see Roaming Client User Guide and Cisco Secure Client.
- Configure the general settings for the roaming devices in your organization. For more information, see Roaming Device Settings.
Configure Your DNS for Local Network
To enable DNS redirection for a roaming device on a protected network, you must configure DNS for the local network and add a network to Secure Access. For more information, see Point Your DNS to Cisco Secure Access.
- Configure the local DNS servers to use Secure Access as the only DNS forwarders.
- Configure the DHCP scope to provide the IPs of the internal DNS servers.
- The local network must allow direct access to either 53/UDP or 443/UDP with a destination of 208.67.222.222.
- The workstation's egress IP must match the configured local DNS server's egress IP's registered network.
Test Your Configured DNS
Run the following commands and confirm that the output contains the same value of the originId.
nslookup -type=txt debug.opendns.com 208.67.222.222
nslookup -type=txt debug.opendns.com [local DNS server IP]
Add Policies
You must add at least two policies that are configured to manage the roaming devices in your organization on-network and off-network.
- Add a policy for roaming devices that send traffic from a protected network.
- Add a policy where the roaming devices are located off the protected network.
- Give the protected network policies higher priority than the off-network policies.
Step 1: Add Networks to On-Network Policies
Add your configured networks to an existing policy or create a new policy and include the network. For more information, see Add a Policy. The on-network policy does not need to enforce content filtering or configure logging. Security filtering is enabled by default.
Step 2: Add Roaming Devices to Off-Network Policies
Add your configured roaming devices to an existing policy or create a new policy and include the roaming device. For more information, see Add a Policy.
Step 3: Order Your Policies
The order of your policies is important. Make the on-network policies have higher precedence than your off-network policies. Give your on-network policies that only contain network identities the highest priority. The on-network policies appear first or before the other policies in your organization.
- On-Network—When the roaming device is on the protected network, the on-network policy takes precedence. The traffic is visible only for the network in the Activity Search report.
- Off-Network—When the roaming device is located off the protected network, Secure Access applies the off-network policy. The Umbrella roaming client or the Cisco Secure Client provides visibility into the traffic sent from the roaming device and Secure Access logs the roaming device traffic in the Activity Search report.
Procedure
Configure the protected network settings for the roaming devices in your organization. For more information, see Roaming Device Settings.
- Navigate to Connect > Essentials > End User Connectivity and click Internet Security.
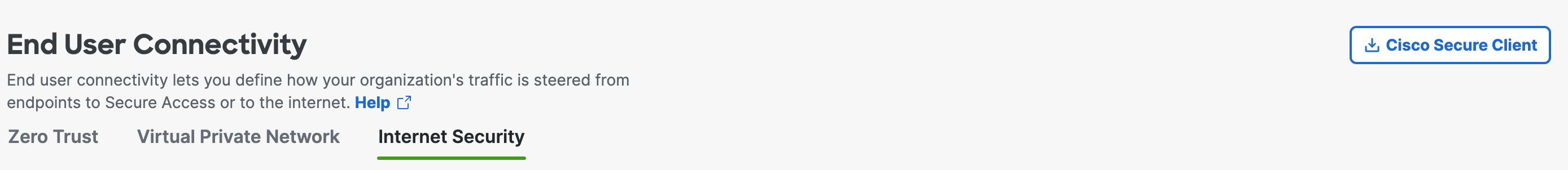
- Expand the Backoff Settings tab. under the Settings section
- Under DNS Backoff Settings, enable DNS protected network.
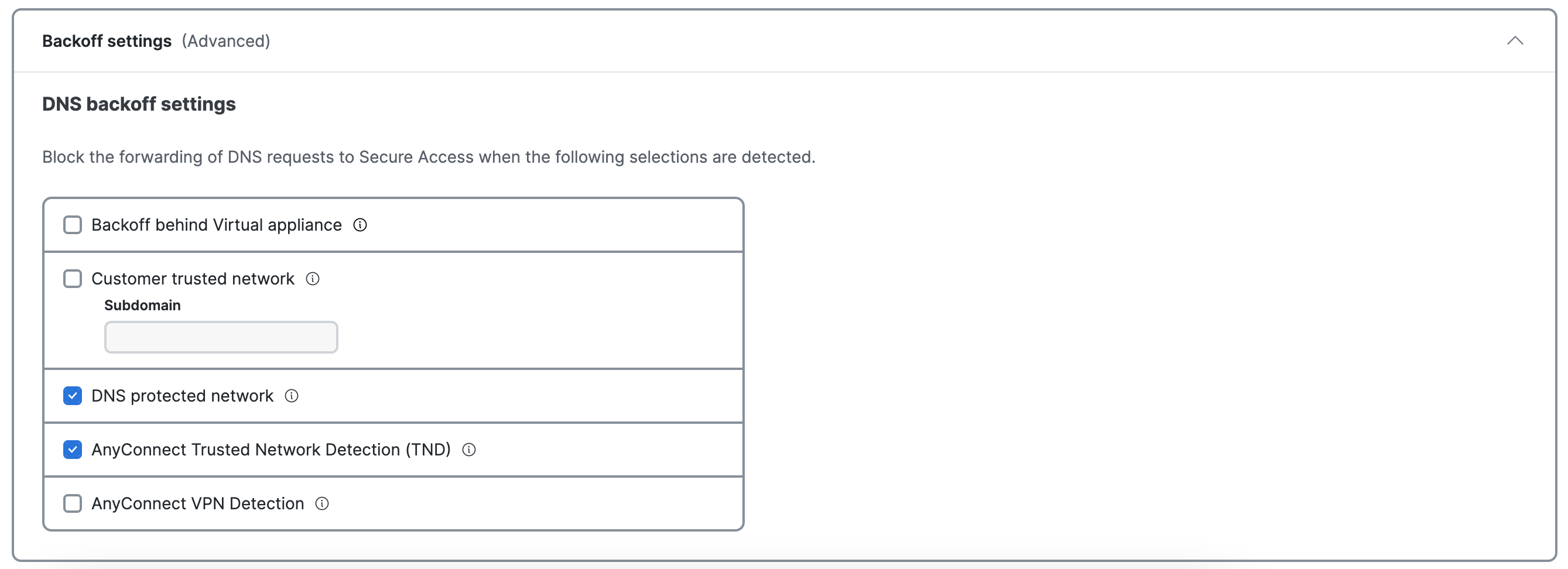
DNS protected network—Disables the DNS-based protection applied by the Umbrella roaming client, and Cisco Secure Client Umbrella module while on a network protected by Secure Access. This includes the intelligent proxy as it is a DNS-based redirect. Relies on the protection of the network for all features. To trigger this setting, network registration and the network must be the higher policy (not same, but higher) and the local DNS server egress network must be the same network registration as straight out from the computer to 208.67.222.222. Having the network in the same organization will not trigger the disabling of traffic redirection.
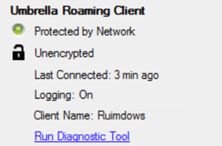
- After DNS redirection is enabled, the roaming client or Cisco Secure Client receives an update from Secure Access. On your roaming device, view the status of the Umbrella roaming client or Cisco Secure Client. After the update is completed, the roaming client's tray icon status displays Protected by Network. The client update may take ten minutes.
Domain Management < Configure Protected Networks for Roaming Devices > Roaming Device Settings
Updated 9 months ago
