Configure Cisco Secure Client Settings
You can configure the Cisco Secure Access Internet Security in Secure Access for end users.
Note: User devices must have the Cisco Secure Client deployed with the Umbrella Roaming Security module for the browsers in the environment.
This guide describes the steps to enable the DNS and web security settings and advanced internet security settings in Secure Access for the end user devices in the organization.
Table of Contents
Prerequisites
- Full Admin user role. For more information, see Manage Accounts.
Procedure
Configure the Cisco Secure Client internet security settings. The advanced internet settings contains several fields that provide additional control over user authentication, traffic bypass, and VPN compatibility.
Configure Advanced Security Settings
- Use Active Directory for Access Policy
- Third Party VPN compatibility
- Client settings
- DNS Backoff Settings
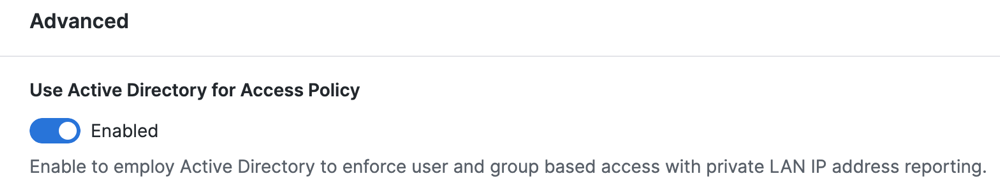
Use Active Directory for Access Policy
Enable the Cisco Secure Client to synchronize users and groups identities with the Secure Access Active Directory (AD) Connector. Secure Access applies Access rules for user identities, which are associated with devices that have deployed the Cisco Secure Client.
- Navigate to Connect > End User Connectivity > Internet Security > General Settings. Enable the Use Active Directory for Access Policy toggle button.
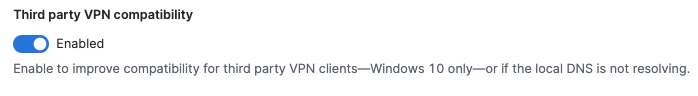
Third Party VPN Compatibility
Improve compatibility for third-party VPN clients on Windows 10 only, or if the local DNS is not resolving resources.
The Cisco Secure Client with the Umbrella Roaming Security module works with most VPN software. However, the Cisco Secure Client with the Umbrella Roaming Security module and other VPN profiles may not resolve local DNS queries correctly on a VPN connection with Windows 10. The local LAN may bind above the VPN, failing to resolve local DNS requests over the tunnel. Select this setting to apply the legacy binding order behavior.
- Enable the Third Party VPN Compatibility toggle button.
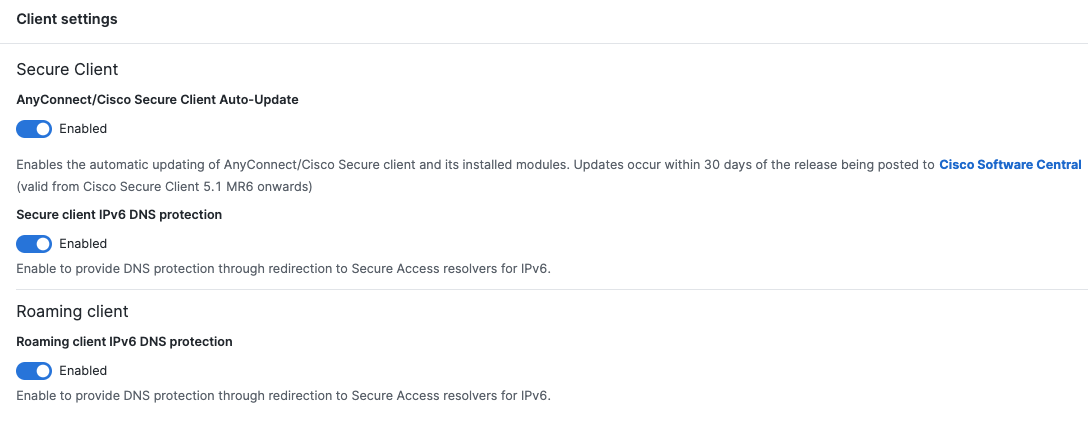
Client settings
- Enable AnyConnect/Cisco Secure Client Auto-Update to enable automatic updating of AnyConnect/Cisco Secure client and its installed modules.
- Enable Secure client IPv6 DNS protection to provide DNS protection through redirection to Secure Access resolvers for IPv6.
- Enable Roaming client to provide DNS protection through redirection to Secure Access resolvers for IPv6.
For more information, see IPv4 and IPv6 DNS Protection Status.
Note: DNS protection over IPv6 DNS64 is not available.
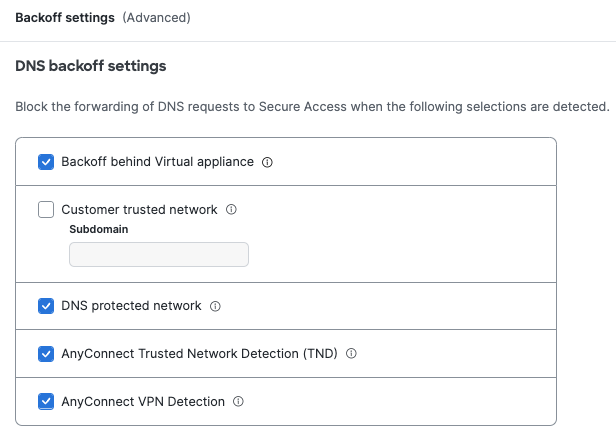
DNS Backoff Settings
Bypass DNS traffic from Secure Access for the following contexts:
- Select Backoff behind Virtual appliance.
When enabled and the Cisco Secure Client detects a Secure Access Virtual Appliance (VA), DNS traffic goes through the local network instead of redirecting to Secure Access. - Select Customer trusted network to disable DNS redirects to Secure Access if the domain name added to the Subdomain field is found on the network and resolves to an RFC-1918 local IP address.
- For Subdomain—enter a domain that Secure Access uses to query the local DNS server.
Note: You must enable Customer trusted network to add the subdomain.
- For Subdomain—enter a domain that Secure Access uses to query the local DNS server.
- Select DNS protected network to disable DNS traffic forwarding while on a network protected by Secure Access.
Relies on the protection of the network. To trigger this setting, you must register the public network in Secure Access and add the network to a rule that has a higher priority than the roaming devices. In addition, the local DNS server egress network must have the same network registration as straight out from the computer to 208.67.222.222. - Select AnyConnect Trusted Network Detection (TND) to disable DNS traffic forwarding from an endpoint to Secure Access if the network is trusted. This setting requires that you have the Trusted Network Detection (TND) setting enabled in the AnyConnect VPN profile for the user devices.
- Select AnyConnect VPN Detection to enable the detection by endpoints that a full-tunnel VPN session is active. When detected, DNS traffic forwarding to Secure Access is disabled. Cisco VPNs only.
Manage Internet Security Bypass < Configure Cisco Secure Client Settings > Manage PAC Files
Updated 6 months ago
