Add a Policy
Through policies, you set the rules as to how Secure Access protects and manages your systems—your identities. Add a policy to Secure Access to provide DNS-layer visibility and enforcement with the ability to proxy risky domains selectively.
Table of Contents
- Step 1: Add a Policy
- Step 2: Select Identities
- Step 3: Determine What You Want This Policy to Do
- Step 4: Setting your Security and Content Details
- Step 5: Set Policy Details
Note: Not all features of the policy wizard explained here are available to all Secure Access packages. To determine your current package, navigate to Admin > Subscription. For more information, see Determine Your Current Package. See also, Cisco Umbrella and Cisco Secure Access packages.
Prerequisites
- Identities are added and configured. See Manage Identities.
- Full admin access to the Secure Access dashboard. See Manage Accounts.
Procedure
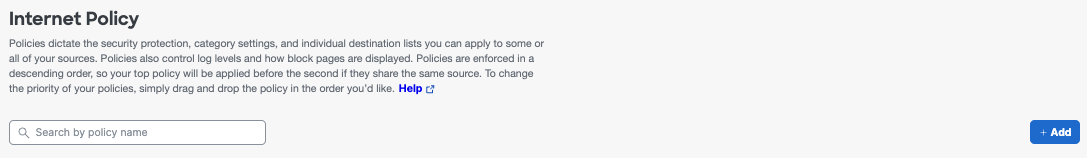
Step 1: Add a Policy
- Navigate to Secure > Internet Policy and click Add.
When the Internet Policy page opens for the first time, it only lists the Default policy. You can add a new policy or edit the Default policy. If you edit the Default policy, the Summary page opens, from which you can edit the Policy.
Note: The Default policy applies to all identities. You cannot remove identities from the Default policy.
Step 2: Select Identities
- Select the identities you wish to apply this policy to and click Next.
This can be any combination of identities available to you. Identity categories, such as AD Computers or Roaming Computers, can be clicked through to choose identities more selectively.
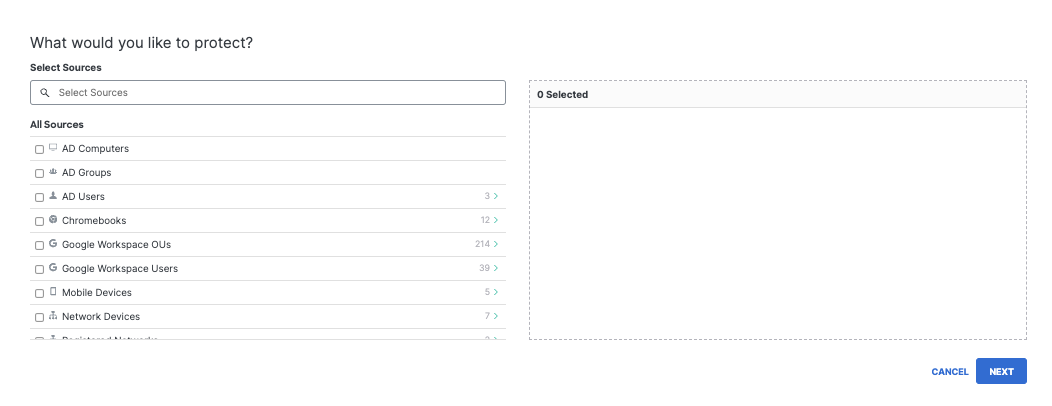
If you have created tags, you can also select these. While listed under identities, a tag is not an identity, but rather a grouping of roaming computer identities. For more information about tags, see Best Practices for Policy Creation.
Step 3. Determine What You Want This Policy To Do
- Select the policy components you'd like to enable.
Selecting an option here makes that component available for configuration in the Policy wizard's later steps. However, selecting an option here does not necessarily activate that feature as some features require additional configuration.
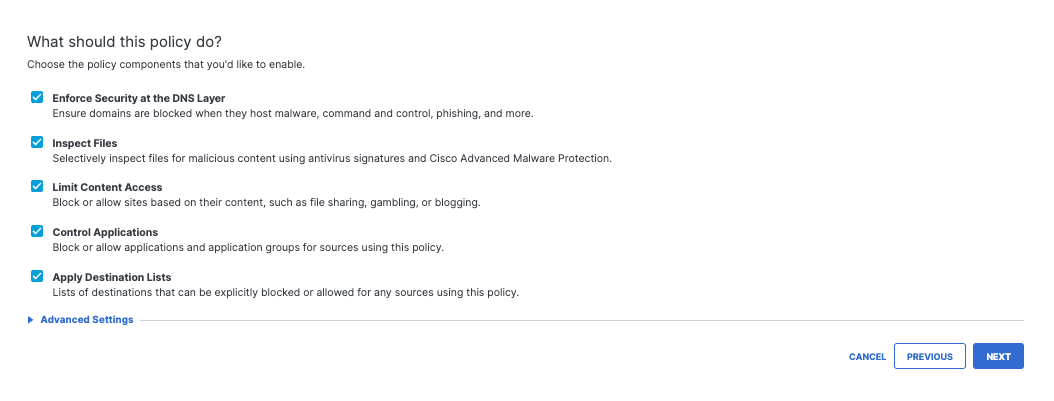
Listed options correspond to policy features:
- Enforce Security at the DNS Layer—These are settings related directly to the blocking of domains based on whether they are malicious and provides a base level of security protection. Recommended.
- Inspect Files—Selectively inspect files in the cloud, not on-premise, so there is no need for additional hardware. The inspection is done with Cisco AMP and an antivirus. Unavailable, if the intelligent proxy is disabled. For more information, see Manage File Inspection.
- Limit Content Access—These settings filter types of content. Recommended.
- Control Applications—These settings block access to applications. Recommended.
- Apply Destination Lists—If you have particular domains you'd like to allow or block, add them to a destination list. There are two by default, block or allow, and you can create more to organize groups of domains. The two defaults are the Global lists, meaning they apply to any policy.
Note: A Global Destination List, whether Block or Allow, applies to all policies and all identities. It is 'global' across all your organization's configurations. To define a specific list, create a new list and add domains only to that list, then apply that list to individual sets of identities.
Advanced Settings
- Expand Advanced Settings to configure the intelligent proxy and related features, SafeSearch, Allow-Only mode, and logging.
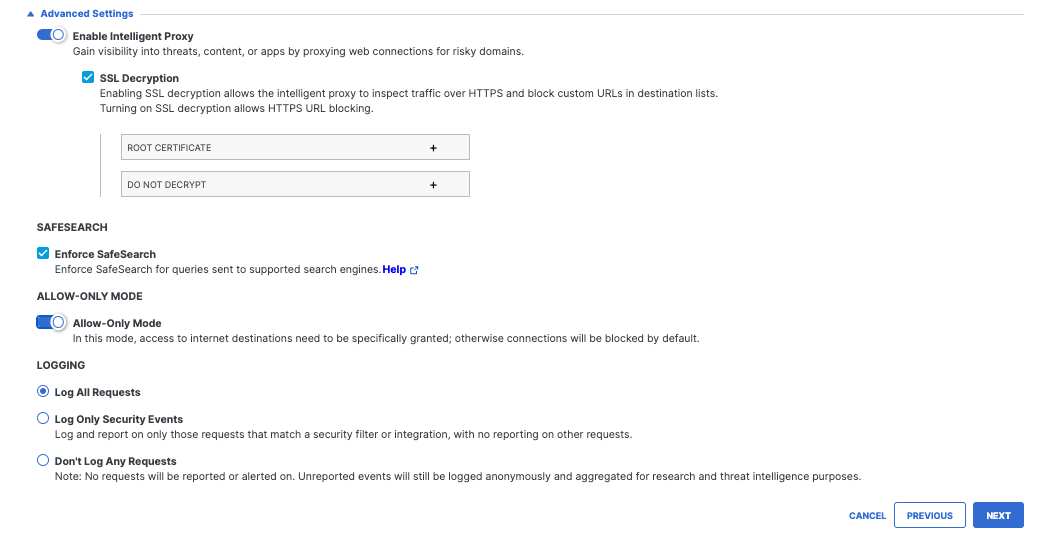
- Enable Intelligent Proxy—Uses Cisco Talos web reputation and other third-party feeds to determine if a URL is malicious. The proxy also uses anti-virus (AV) engines and Cisco Advanced Malware Protection (AMP) to inspects files before they are downloaded. When disabled, File inspection is also disabled. For more information about the intelligent proxy, see Manage the Intelligent Proxy.
- SSL Decryption—Allows the intelligent proxy to inspect traffic over HTTPS and block custom URLs in destination lists. For more information, see SSL Decryption Requirements and Implementation.
- Root Certificate—Download and install the Cisco Umbrella root certificate on all computers that are a part of this policy. For more information, see Manage the Cisco Umbrella Root Certificate.
- Selective Decryption—Create a list of content categories to exclude from inspection by the intelligent proxy. For more information, see Selective Decryption.
- Enable IP-Layer Enforcement—For roaming client identities only, tunnels suspect IP connections to gain visibility into threats that bypass DNS lookups. For more information, see Add IP Layer Enforcement.
- Enforce SafeSearch—A feature of the major search engines that restricts and filters explicit images and results. Secure Access provides you with the ability to enforce traffic to Google, YouTube, and Bing. For more information, see Enable SafeSearch.
- Allow-Only mode—Select in cases where you wish to allow access to a small subset of domains and block all other domains. Because the result of enabling this feature is to effectively block access to the internet except for that part you've defined as "allowable", we recommend caution if you are enabling this feature.
Note: This mode only applies to DNS requests, and not HTTP/HTTPS requests.
Logging settings are:
- Log All Requests—For full logging, whether for content, security or otherwise
- Log Only Security Events—For security logging only, which gives your users more privacy—a good setting for people with the roaming client installed on personal devices
- Don't Log Any Requests—Disables all logging. If you select this option, most reporting for identities with this policy will not be helpful as nothing is logged to report on.
For more information about managing your logs, see Manage Your Logs.
- Click Next.
When you click Next you'll see a progress meter with the number of steps remaining until you've fully configured the policy. Available steps correspond to your policy component selections.
Step 4. Setting Your Security and Content Details
Step 4a. Configure Security Settings
These settings determine which categories of security threat Secure Access blocks. For more information about security category, see Manage Threat Categories.
When you first access Threat Categories, default settings are applied. The blue shield icon indicates a selected and enabled security category. You can leave this setting as is, select a different setting or edit settings and create a new one if needed.
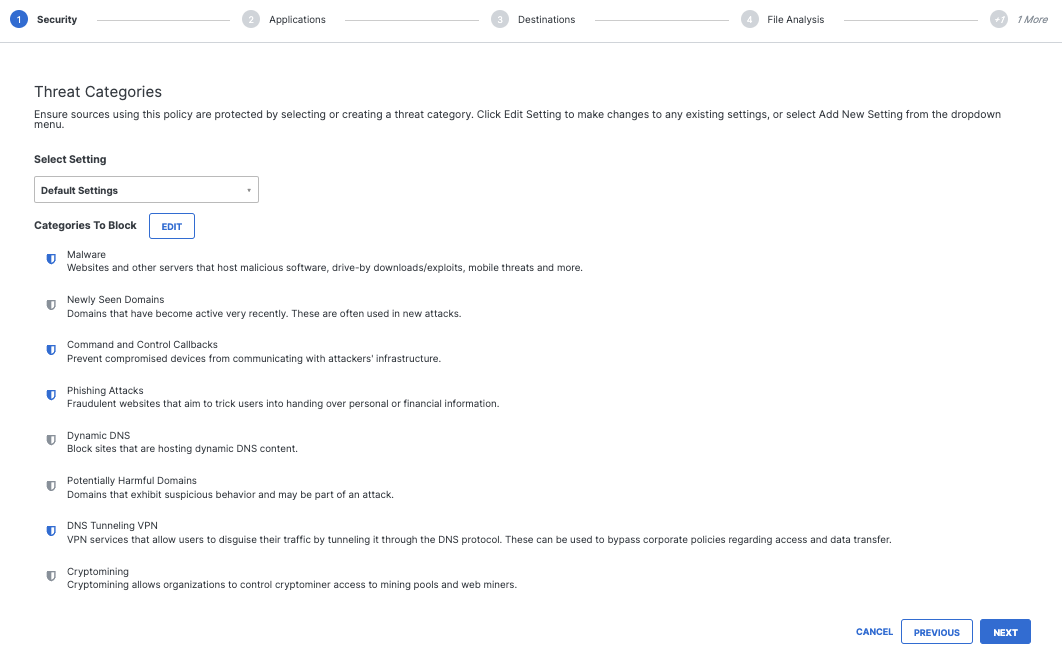
- To edit settings, click Edit, select or clear security categories, and then click Save.
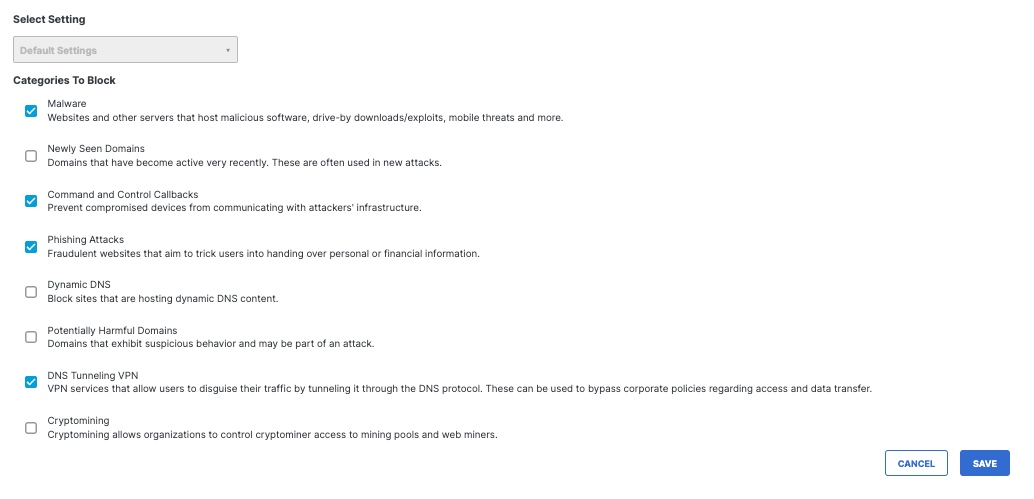
As an alternative to clicking Edit, you can select preconfigured groupings of security settings or create a new setting that you can reuse.
- From the Select Setting drop-down list, choose a security setting or click Add New Setting.
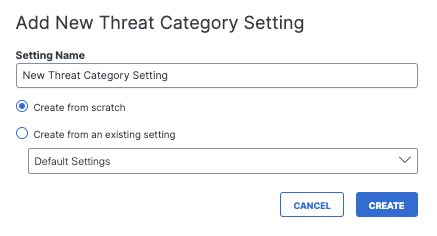
If you choose Add New Setting, a window appears allowing you to add a new setting.
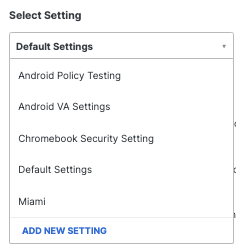
- Give your new setting a meaningful name, select how it is created and then click Create.
- If you select Create from scratch, select security settings and click Create.
Your security setting is added to the drop-down list.
Step 4b. Configure Application Settings
Select applications to block access to them when they represent an unacceptable risk or when their functionality is inappropriate.
- Select application categories to be blocked or expand a category to choose individual applications.
Note: SSL Decryption must be enabled. - Click Next.
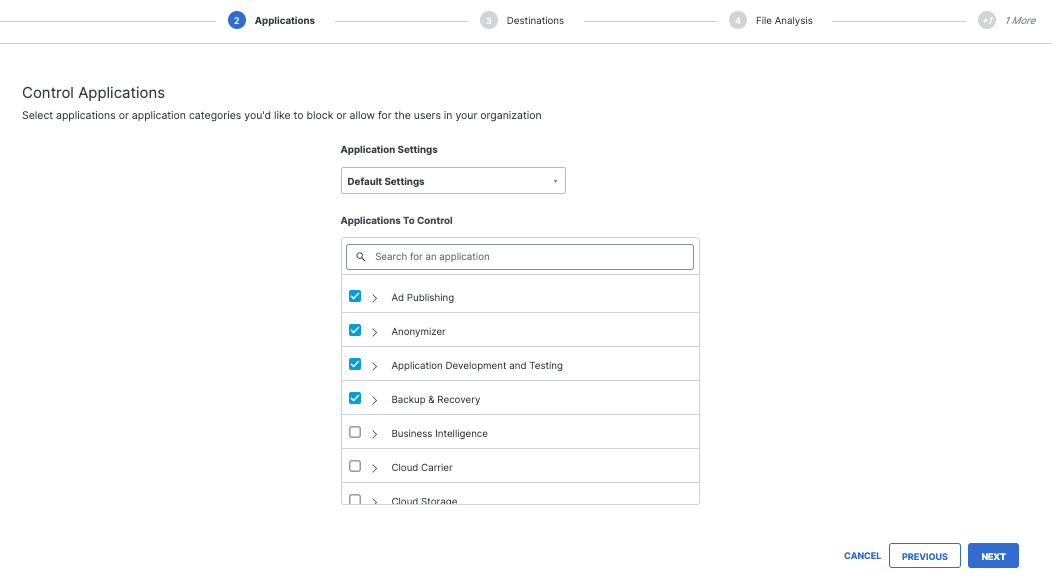
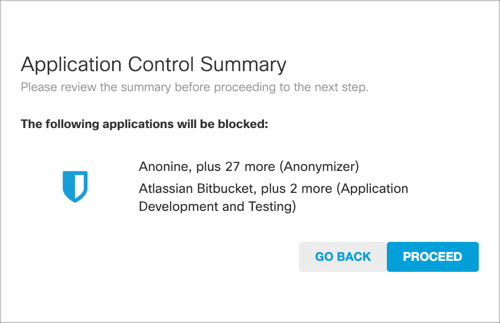
- Click Proceed to confirm your Application selections.
Step 4c. Configure Destination Lists
Destination lists allow for the customization of filtering by creating a list of domains that are explicitly blocked or allowed.
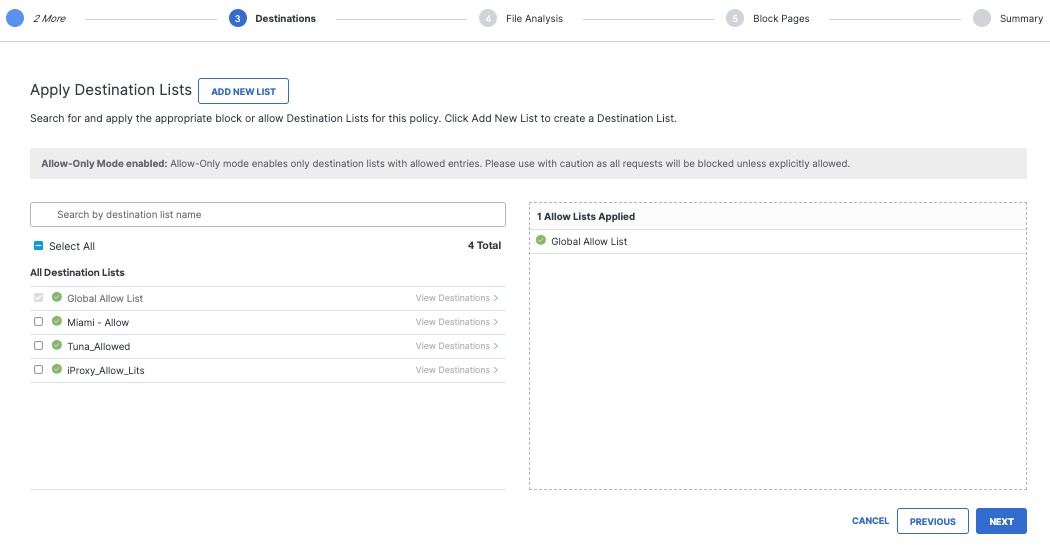
Creating a destination list is simple: first, pick the type of list you want, then add the domains you would like to have allowed or blocked and give the list a name.
For more information, see Manage Destination Lists.
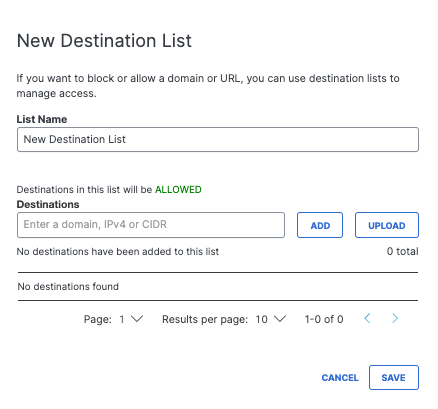
Note: Destination lists are not saved until you click Save, although it appears in the list view after entering it.
An IP Address or CIDR of IP Addresses (Roaming Client Only)
This feature applies to IP Layer Enforcement via the roaming client only, and will not override DNS-based blocks sourced from malicious IP information. It requires that the roaming client is installed on the identities for this feature in the policy.
For Destination Allow Lists only (for now), you can add an IP address or a block of IP addresses. The format for the block of IP addresses is standard CIDR notation.
The size of the CIDR cannot exceed a /8, otherwise, you'll receive this error:
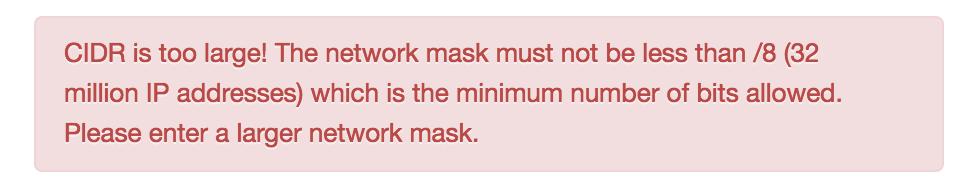
If you enter an invalid subnet mask, such as 24.24.24.24/1000000, the IP will be added but the network notation will be ignored.
Otherwise, add any destination that you'd like to ensure isn't blocked now or in the future.
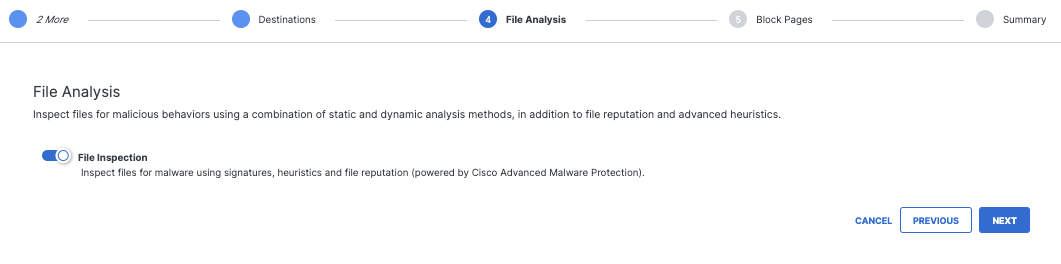
Step 4d. Configure File Analysis
File Analysis lets you enable file inspection, which inspects and blocks malicious files through the use of Cisco Malware Protection (AMP) and antivirus. See also Enable File Inspection.
- Enable File Inspection.
- Click Next.
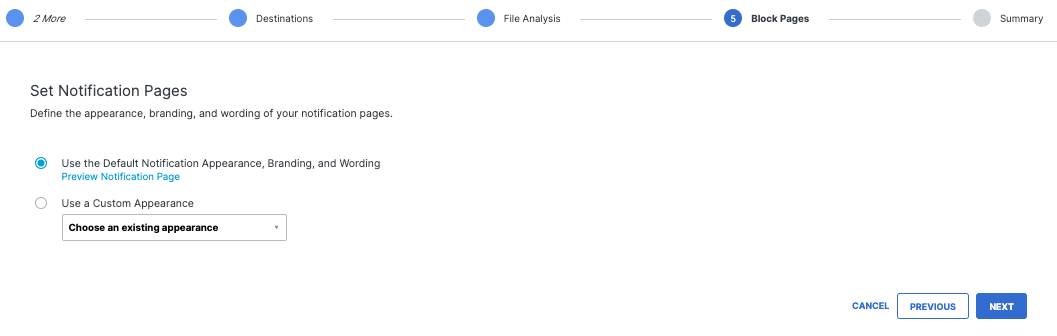
Step 4f. Configure Notification Pages
Notification Page Settings let you configure a block page that appears when a request is made to access a blocked page. You can also create a bypass so that access can be granted to the block page. You can customize the block page's appearance and redirect to a custom domain.
Note: Not all categories can be bypassed. If a user is blocked for a Security or Malware category, the site is considered malicious and should not be accessed under any circumstances. If you think a domain shouldn't be blocked, contact Support.
If you'd like to know more about a block or have us review it in more detail, open a case by contacting Secure Access Support with information about the domain and our support and security teams will review it.
Notification Page Settings
If you do not wish to change anything, just use the Default Notification Appearance, but this setting also allows for the customization of the block page.
To edit an existing Notification Page:
- Expand the drop down menu under Use a Custom Appearance, and click the page you wish to edit. Next to the name, click the Edit pen icon.
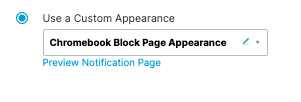
- Select Use a Custom Appearance, then choose Add New Appearance from the drop-down list.
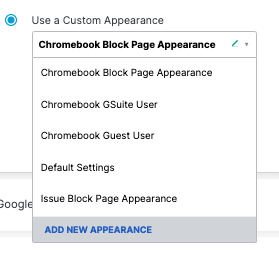
When you create or edit a page, give your settings an easy to remember name, such as "Corporate Block Policy."
Choose a generic message across all block pages, or customize the message per type of block page by selecting whether Blocked requests should be treated the same or differently. If you set a custom message, you may insert the [domain] variable into a custom message, which is substituted with the actual domain name that the end user attempted to browse to. You may also insert the [client_ip] variable, which shows the external IP address of the client that is hitting the block page.
If you set a custom message, you may insert the [domain] variable into a custom message, which is substituted with the actual domain name that the end user attempted to browse to
The block can also redirect to a custom URL.
If not redirecting to a custom URL, a contact form can be added to allow blocked users to contact the administrator at the email provided.
Finally, a custom logo can be uploaded to be displayed on the block page in place of the Secure Access logo.
Once you've set your block page and bypass settings, click Next.
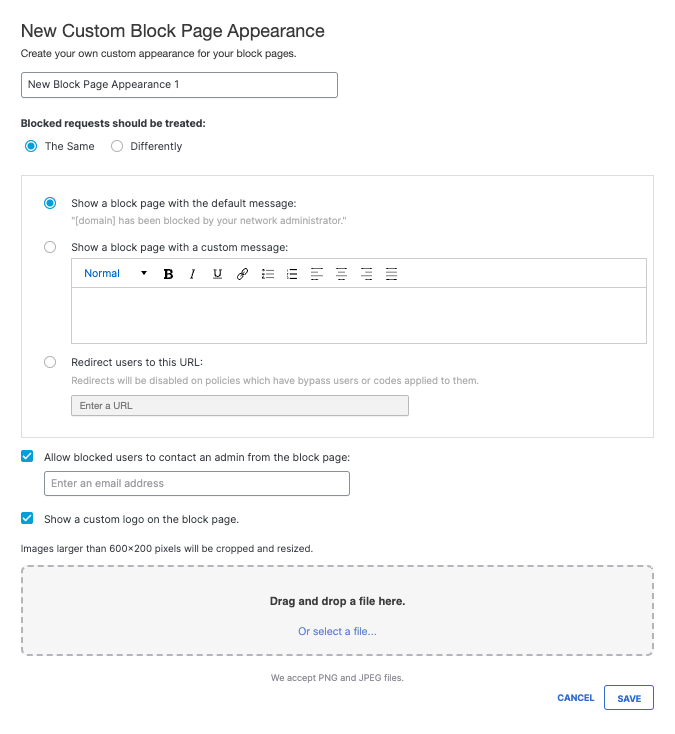
Step 5: Set Policy Details
Lastly, you'll reach the Policy Summary. It covers all of the modifications to the policy you just made. If you want to change anything, click the relevant Edit button and you'll jump right back to that step, or disable the feature directly from the Summary screen. When you've made the change, you can jump back to the summary directly without having to click through all the other steps (neat, right?).
- Give your policy a meaningful name.
- Click Edit to go back and modify settings.
- Click Save.
Your policy is complete. As you add identities and configurations for Secure Access, you may need to tweak your policy. When you open an existing policy, the Summary screen opens, and you can jump between steps in order to make the change you need to make immediately without having to do redo the entire wizard.
Get Started With Internet Access Policy < Add a Policy > Policy Settings
Updated 7 months ago
